| Bytes | Lang | Time | Link |
|---|---|---|---|
| 011 | BrainChild ASM | 250115T003924Z | ATaco |
| 4233 | SqueezeL | 250113T031425Z | AlephSqu |
| 004 | Emotinomicon | 161201T160504Z | Linnea G |
| 001 | Pip | 230212T205801Z | The Thon |
| 008 | Swift | 240308T225620Z | macOSist |
| 011 | Python | 240308T060259Z | Stefan P |
| 016 | Tamsin Compiler | 240222T175444Z | Mukundan |
| 024 | C gcc | 231013T160525Z | The Empt |
| 001 | Uiua | 231013T020301Z | chunes |
| 001 | Notepad | 210429T170736Z | Makonede |
| 004 | ><> Fish | 230603T213043Z | chunes |
| 002 | Thunno 2 | 230603T181621Z | The Thon |
| 012 | Fortran GFortran | 230208T031026Z | roblogic |
| 012 | Borland C on Windows | 161201T075559Z | user5898 |
| nan | 230110T195410Z | The Thon | |
| 002 | Vyxal | 230108T142724Z | The Thon |
| 1514 | SNOBOL4 CSNOBOL4 | 220927T051543Z | 鳴神裁四点一号 |
| 003 | Knight | 220804T022739Z | 97.100.9 |
| 012 | JavaScript full program | 220803T060031Z | Leaf |
| 002 | PARI/GP | 220803T054524Z | alephalp |
| 002 | Knight | 220803T051436Z | Bubbler |
| 001 | Pyke | 161130T202636Z | Blue |
| 218 | Taxi | 170729T014902Z | The Fift |
| 001 | APOL | 211211T160058Z | Ginger |
| 019 | SNOBOL4 CSNOBOL4 | 211027T134239Z | user1004 |
| 002 | Braingolf | 170517T155823Z | Mayube |
| 120 | .mmo MMIX executable | 210429T220851Z | NoLonger |
| 004 | Julia | 210514T141114Z | MarcMush |
| 002 | Barrel | 210514T115453Z | LorenDB |
| 044 | EmojiCoder | 210514T083014Z | Wasif |
| 005 | C | 210429T171821Z | Makonede |
| 039 | CSASM v2.2.1.2 | 210322T195114Z | absolute |
| 054 | C gcc | 210226T090148Z | user9275 |
| 004 | Phooey | 210207T014231Z | EasyasPi |
| 004 | ThumbGolf | 210206T230249Z | EasyasPi |
| 002 | 05AB1E | 210206T234803Z | Makonede |
| 000 | Pxem Filename 5 bytes Contents | 210206T132157Z | user1004 |
| 002 | BrainfuckX and small s.c.r.i.p.t. etc polyglot | 161130T220503Z | wyldstal |
| 049 | Haskell | 201018T140230Z | Wheat Wi |
| 001 | Keg | 190607T135111Z | user8505 |
| 002 | CJam | 161201T194658Z | Erik the |
| 014 | Trigger | 190531T210823Z | MilkyWay |
| 037 | Intercept 1.1 | 190319T000817Z | Benjamin |
| 001 | Japt | 190319T005235Z | Cortex |
| 007 | Perl 6 | 190319T001913Z | bb94 |
| 003 | Gol><> | 190301T010559Z | KrystosT |
| 005 | Ink | 190218T000552Z | Sara J |
| 028 | Rust | 180720T233455Z | Esolangi |
| 004 | Flobnar | 180812T074609Z | Esolangi |
| 007 | Lost | 180815T002301Z | Jo King |
| 001 | Pyt | 180210T214327Z | mudkip20 |
| 004 | Wumpus | 180210T204443Z | Martin E |
| 012 | Kotlin script .kts | 161130T213434Z | F. Georg |
| 235 | Chip | 180117T162459Z | Phlarx |
| 003 | Retina | 180116T153938Z | Martin E |
| 202 | INTERCAL | 170914T141949Z | KSmarts |
| 004 | Chip8 | 171006T165208Z | 12Me21 |
| 005 | BrainFlump | 170914T102055Z | Mayube |
| 027 | Java 7 | 161130T203643Z | Poke |
| 006 | Add++ | 170606T200810Z | caird co |
| 000 | Baby Language | 170427T224010Z | user6213 |
| 003 | Fourier | 170412T111621Z | Beta Dec |
| 018 | C gcc | 170412T110510Z | Bijan |
| 019 | C | 170411T195722Z | Albert R |
| 022 | C | 161201T211542Z | user5898 |
| 004 | Alice | 170411T131847Z | Martin E |
| 003 | tcl | 170207T004527Z | sergiol |
| 004 | Commodore 64 Basic | 161130T234101Z | Mark |
| 072 | C# | 170207T082703Z | Metoniem |
| 006 | SmileBASIC | 170125T053949Z | 12Me21 |
| 002 | TIBasic | 161206T153926Z | Timtech |
| 002 | PowerShell | 161130T202652Z | AdmBorkB |
| 011 | ForceLang | 161201T150224Z | SuperJed |
| 014 | Ruby | 161204T143504Z | Vasu Ada |
| 002 | Shell | 161204T132303Z | Ronsor |
| 003 | MATLAB | 161203T182941Z | Stewie G |
| 004 | JavaScript | 161130T204428Z | ETHprodu |
| 009 | Lua | 161203T014033Z | Myria |
| 002 | Pyth | 161202T215312Z | Erik the |
| 009 | Groovy | 161130T214751Z | Magic Oc |
| 002 | Minecraft | 161202T165652Z | user6019 |
| 019 | C++ | 161202T081918Z | Snowfire |
| 004 | Minecraft | 161130T224630Z | Pavel |
| 006 | Inform 7 | 161201T213107Z | Draconis |
| 022 | Ceylon on JVM | 161201T213031Z | Paŭlo Eb |
| 043 | ASP VBScript | 161201T154330Z | Mario |
| 004 | TI83 Hex Assembly | 161201T192053Z | habs |
| 009 | Java2K | 161201T173836Z | mbomb007 |
| 000 | huh? | 161201T172122Z | mbomb007 |
| 004 | Minkolang v1.5 | 161201T165928Z | user4180 |
| 005 | Math++ | 161201T160350Z | SuperJed |
| 010 | PHP | 161201T155504Z | aslum |
| 018 | HSPAL | 161201T155005Z | SuperJed |
| 012 | PHP | 161130T221200Z | Mario |
| 001 | Microscript II | 161201T150612Z | SuperJed |
| 015 | TSQL | 161201T153514Z | Nelson |
| 017 | Thue | 161201T153156Z | SuperJed |
| 022 | C# | 161201T151259Z | Yodle |
| 007 | Mouse2002 | 161201T152443Z | cat |
| 020 | C89 with GCC/Clang | 161201T143454Z | cat |
| 002 | Microscript | 161201T150923Z | SuperJed |
| 011 | Randwork | 161201T150613Z | mbomb007 |
| 002 | Bash procpsng | 161130T203603Z | Riker |
| 007 | R | 161201T135749Z | djhurio |
| 001 | Actually | 161201T102246Z | user4594 |
| 004 | QBIC | 161201T102049Z | steenber |
| 001 | MATL | 161130T215041Z | Luis Men |
| 005 | Marbelous | 161201T085802Z | Martin E |
| 003 | Brachylog | 161201T075042Z | Fatalize |
| 003 | Befunge 93 and 98 | 161130T202631Z | user6213 |
| 013 | Swift 3 | 161201T040636Z | Daniel |
| 002 | APL | 161201T033045Z | ren |
| 013 | Perl 6 | 161201T025945Z | Brad Gil |
| 004 | Clojure | 161201T002908Z | Carcigen |
| 010 | PHP | 161130T233022Z | UTF-8 |
| 021 | C | 161130T220052Z | Sake |
| 002 | Wirefunge | 161130T220856Z | wyldstal |
| 001 | R | 161130T215301Z | chrki |
| 003 | Cubix | 161130T213145Z | ETHprodu |
| 003 | x86/amd64 machine language Pentium or higher | 161130T213516Z | ceilingc |
| 002 | Jelly | 161130T203759Z | Pavel |
| 004 | Batch | 161130T210004Z | Neil |
| 006 | Mathematica | 161130T211403Z | Greg Mar |
| 003 | ><> | 161130T205310Z | Blue |
| 001 | sh + procps | 161130T204002Z | user6213 |
| 001 | Japt | 161130T210206Z | ETHprodu |
| 029 | Python 2 | 161130T202412Z | Pavel |
| 008 | JavaScript | 161130T205819Z | Neil |
| 001 | WinDbg | 161130T205815Z | milk |
| 000 | Shellscript as implemented by ttyrec | 161130T205145Z | user6213 |
| 005 | Labyrinth | 161130T204145Z | Martin E |
| 003 | Ruby | 161130T204611Z | Martin E |
| 005 | Zsh | 161130T203122Z | betseg |
| 002 | 05AB1E | 161130T202907Z | Magic Oc |
| 011 | Python 2 | 161130T203045Z | Blue |
| 005 | Perl | 161130T202203Z | user6213 |
BrainChild ASM, 11 bytes
asm {
reada
incb
l: reada
writeb
deca
deca
deca
deca
jbnza
}
Hex-dump of bytecode
0 1 2 3 4 5 6 7 8 9 A B C D E F
00000000: 27 16 00 00 27 2A 17 17 17 17 0F | '...'*.....
Outputs a random amount of garbage until the first frame (When it receives interrupt code 4). Constant values take 4 bytes plus an instruction to use, and labels are padded to 4 bytes, so they're avoided throughout the program where possible
BrainChild, 39 bytes
while(4!=getchar()||!int i++)putchar(i)
Outputs a random amount of garbage until the first frame
SqueezeL, ceil(4 * 2/3) = 3 bytes
(zor
Returns a random float in [0, 1), which is implicitly printed.
Emotinomicon, 4 bytes
😀😅🎲⏬
Explanation:
😀😅🎲⏬
😀 push 0. Stack: [0]
😅 push 1. Stack: [1]
🎲 random[pop;pop]. Stack: [1 or 0]
⏬output
Swift, 8 bytes
[][0]
Literally all this does is create an empty array (which the compiler miraculously infers to be of type [Any]) and attempts to access its first element, which obviously does not exist because the array is empty. Unlike some other languages I can name, Swift actually makes sure you don't try to use things that don't exist, and so this subscript calls fatalError(_:file:line:), which (among other, more useful things) prints out memory addresses, thereby meeting the criteria for non-determinism.
Python, 11 bytes
1/(id(2)%3)
Sometimes it outputs nothing, sometimes it outputs a ZeroDivisionError message.
Matches @Blue's print id(1), but that needs parentheses in Python 3, making it 12 bytes there.
Tamsin (Compiler), 16 bytes
main=any@'\xf0'.
Explanation
main= # output
any # read 1 utf-8 char
@ # from
'\xf0'. # '\xf0'
The Tamsin compiler produces C code that omits out-of-bounds checks during the reading of UTF-8 characters. Consequently, upon encountering \xf0, it proceeds to read an additional three bytes beyond the string's limit which are also output.
The Tamsin interpreter (used by TIO) does not suffer from this issue (it simply throws an assertion error).
C (gcc), 24 bytes
main(){printf("%s",.0);}
My favourite, since the warning messages in stderr also get corrupted slightly.
Notepad, 1 keystroke
F5
Pressing F5 inserts the time and date in the format (h)h:mm XM (m)m/(d)d/yyyy. For example: 12:00 AM 1/1/1970
><> (Fish), 4 bytes
1n0x
Prints 1, then prints 0 or 1 randomly, as the x will cause the instruction pointer to move either left or right.
Fortran (GFortran), 12 bytes
print*,i
end
Try it online! Fortran has a bunch of "random" functions, ironically all deterministic, like RAND, needing all kinds of complicated seeds to make a mathematically pure random distribution. But in this code I just grab an uninitialized integer i, and print whatever is in that memory location.
Borland C on Windows, 12 bytes
m(){puts();}
I rewrote it because they said it's possible to use one function.
The compiler doesn't check the argument so it compiles it; but puts sees an unknown address and begins to print what that address points to until it finds the byte 0x00. It would not work if that address was out of memory, but here it prints something.
Thunno, \$ 4 \log_{256}(96) \approx \$ 3 bytes
(actually 3.29 bytes but that doesn't show up on the leaderboard)
9RZw
Outputs a random integer from 0 to 8:
9Rgetsrange(0, 9)(i.e.[0, 1, ..., 8])Zwgets a random element of that list
JavaScript (full program), 12 bytes
throw is much smaller than console.log() or process.stdout.write(), it does halt execution, but that's not an issue.
throw Date()
PARI/GP, 2 bytes
\s\s prints the state of the PARI stack and heap, which is non-deterministic.
Example output:
Top : 7fadf82bd000 Bottom : 7fadf7b1be00 Current stack : 7fadf82bcfb8
Used : 9 long words (0 K)
Available : 999991 long words (7808 K)
Occupation of the PARI stack : 0.00 percent
1 objects on heap occupy 9 long words
10 variable names used (10 user + 0 private) out of 65535
Knight, 2 bytes
`R
` Run as a shell command:
R A random integer
The non-deterministic output is to stderr. The C interpreter implicitly converts the number to string and tries to run it as a shell command. With very high chance (if not 100%), such a command or executable does not exist in PATH, and an error message that looks like sh: <some random number>: command not found is printed to stderr.
This is shorter than the straightforward O R which prints the random number to stdout.
Taxi, 222 220 218 bytes
Go to Heisenberg's:w 1 r, 3 r, 1 l.Pickup a passenger going to The Babelfishery.Go to The Babelfishery:s 1 r, 1 l.Pickup a passenger going to Post Office.Go to Post Office:n, 1 l, 1 r.Go to Taxi Garage:n 1 r, 1 l, 1 r.
Prints a random number. The spec does not give any details on what number should be. The last statement can be omitted (producing 184 bytes) if you don't mind the code giving an error after printing the output.
APOL, 1 byte
≀
This is just the random float instruction, the result of which is implicitly printed.
SNOBOL4 (CSNOBOL4), 19 bytes
output =date()
end
Are there any other ways to obtain a random value in this language?
Braingolf, 2 bytes
2r
Pushes 2 to the stack, then pushes a random number between 0 and the last item on the stack (2), ie randomly selects either 0 or 1. Implicitly prints the last item on the stack (the random number)
.mmo (MMIX executable), 128 120 bytes
(xxd --jelly)
00000000: 98090100 98010001 00000100 e3ff0130 Ƭµ¢¡Ƭ¢¡¢¡¡¢¡ẉ”¢0
00000010: 00000103 e3ff0140 00000303 e3ff0140 ¡¡¢¤ẉ”¢@¡¡¤¤ẉ”¢@
00000020: e0012000 87000100 ef00a0a0 eb004040 ṭ¢ ¡⁷¡¢¡ṁ¡ɦɦḟ¡@@
00000030: a7000100 00000601 98020008 00000150 ʂ¡¢¡¡¡©¢Ƭ£¡®¡¡¢P
00000040: 00000000 00000002 20000000 98020008 ¡¡¡¡¡¡¡£ ¡¡¡Ƭ£¡®
00000050: 00000002 2f646576 2f72616e 646f6d00 ¡¡¡£/dev/random¡
00000060: 980a00ff 00000000 00000100 980b0000 Ƭ½¡”¡¡¡¡¡¡¢¡Ƭ¿¡¡
00000070: 00000000 980c0001 ¡¡¡¡Ƭ€¡¢
Outputs two random characters in range @-_ to stdout.
Explanation
98090100 lop_pre 1,0 (preamble, mmo v1, 0 tetras)
98010001 lop_loc 0,1 (next tetra says where to load)
00000100 (256)
E3FF0130 SETL $255,random
00000103 TRAP 0,Fopen,3 (open fd 3 for bin read from /dev/random)
E3FF0140 SETL $255,data
00000303 TRAP 0,Fread,3 (read two bytes of data)
E3FF0140 SETL $255,data (set up $255 for writing it back out)
E0012000 SETH $1,#2000 (we know where the data is)
87000100 LDWU $0,$1,0 (read those bytes from memory)
EF00A0A0 ANDNL $0,#A0A0 (ensure C0 control or @-_)
EB004040 ORL $0,#4040 (ensure @-_)
A7000100 STWU $0,$1,0 (write them back to memory)
00000601 TRAP 0,Fwrite,StdOut (write two bytes out)
98020008 lop_skip 8 (encodes the next two tetras)
TRAP 0,Halt,0 (halt)
random OCTA fname (argument 1 of fopen: ptr to filename)
00000150 (cont)
00000000 OCTA BinaryRead (argument 2: mode)
00000002 (cont)
20000000 data OCTA Data_Segment (argument 1 of fread/fwrite: buffer addr)
98020008 lop_skip 8 (encodes cont + start of next)
OCTA 2 (argument 2: amount)
00000002 (cont)
2F646576 fname BYTE "/dev"
2F72616E BYTE "/ran"
646F6D00 BYTE "dom\0"
980A00FF lop_post 255 (one global register)
00000000
00000100 (start at 0x100)
980B0000 lop_stab (symbol table)
00000000 (no symbols)
980C0001 lop_end 1 (one symtab tetra)
Basically, this reads two characters from /dev/random, then, after a bit of munging to ensure they're printable, dumps them to stdout.
I also used lop_skip to cut two tetras from the code.
EmojiCoder, 44 bytes
🙈🔢🌚🌝🌚🌚🌚🌚🌚🌝
✋
Push some random integer between 0 to 65 (chosen randomly) and output top of stack.
CSASM v2.2.1.2, 39 bytes
func main:
extern Random.Next
print
ret
end
CSASM has a built-in System.Random object that gets initialized to new System.Random() when CSASM.Core.Sandbox.Main(System.Reflection.MethodInfo, int, string[]) is called.
The default System.Random constructor initializes the seed to Environment.TickCount, which is different every time the executable runs.
extern Random.Next calls Random.Next() on the aforementioned object, which returns a positive int value.
C (gcc), 63 54 bytes
main(){int a;for(char*b;a=3;b++)for(;a;a--)printf(b);}
I can't even remember how this one works.
Down to 54 bytes by 2x-1.
Puts instead of printf creates triangle patterns instead, but I think they're boring.
Phooey, TIO version, 4 bytes
<2$i
Abuses a bug to print the frame pointer.
This is because the tape does not wrap, so the tape just underflows to the stack.
<2 moves the pointer 16 bytes back, $i prints as an integer.
Very dependent on the version of the binary.
Phooey, proper version, 5 4 bytes
~t$i
~t stores the Unix time to the tape, and I already explained $i.
ThumbGolf, 4 bytes
Machine code:
de78 de20
Assembly:
// Include ThumbGolf wrapper macros
.include "thumbgolf.inc"
.globl main
.thumb_func
main:
// Read random integer into r0
rand r0 // udf #0170
// Print to stdout in base 10
puti r0 // udf #0040
// Not required to exit, so just crash
Internally, ThumbGolf uses /dev/urandom, so this is guaranteed to be nondeterministic.
Alternative version, 2 bytes
Machine code:
de21
Assembly:
// Include ThumbGolf wrapper macros
.include "thumbgolf.inc"
.globl main
.thumb_func
main:
// print address of argv
// printf("%i", (int)argv)
puti r1 // udf #0041
// exit by crash
Prints the memory address of argv which is almost guaranteed to be dynamically allocated, and therefore, nondeterministic.
However, it is context sensitive unlike the 4 byte solution.
05AB1E, 2 bytes
Any program matching /^[ATт₁-₆]Ω|ž[a-g]$/ will give nondeterministic output. There are, of course, infinitely many programs that can do this, but these are all the two-byters. Unfortunately, I could not find a one-byter... :(
Explanation
The ones starting with ž are constants. The ones used here are time constants - ža, žb, žc, žd, že, žf, and žg are hours, minutes, seconds, microseconds, day, month, and year, respectively. The ones ending in Ω pick a random element (for lists), character (for strings), or digit (for integers) from top of stack. The one-byte commands that I could find that push something with more than one distinct element/character/digit were A, T, т, ₁, ₂, ₃, ₄, ₅, and ₆, which push abcdefghijklmnopqrstuvwxyz, 10, 100, 256, 26, 95, 1000, 255, and 36, respectively.
Pxem (Filename: 5 bytes; Contents: 0 byte)
- Filename:
x.r.n - File content is empty.
Explaination
xpushes an ascii code of the character (120) as a signed integer..rpops 120 to push back one of 0-119..npops the integer to output as a decimal.
BrainfuckX and small s.c.r.i.p.t. (etc) polyglot - 2 bytes
?.
? - Randomize the value in the current cell
. - Send current cell to stdout
Haskell, 49 bytes
import Unsafe.Coerce
main=putStr[unsafeCoerce(+)]
Unfortunately this seems to always outputs the same thing on TIO (I don't quite know why, but I have some guesses), so if you want to try it you should run it locally.
I've only tested this on Linux and OSX. I make no guarentees about Windows. If you are having trouble getting it to work on Linux I would be interested to know.
Explanation
What is unsafeCoerce?
This answer relies on unsafeCoerce. This function is a bit of magic, so first we are going to have to do a quick intro to Haskell's type system.
Haskell has something called type erasure. This means that the compiler checks all the types to make sure that nothing in the program is called on the wrong type. Once it is done with that there is no need to actually store type information any more, so Haskell erases it. So at runtime all data is the same and just relies on the fact that we already checked all the types before hand so nothing goes horribly wrong.
unsafeCoerce is a function that lies to the type checker. It tells it that it can take any input and produce any output; it's type is
forall a. forall b. a -> b
But it does nothing, it gives back the input exactly as it got it. So if you take a string like "abcd" and coerce it to an int using unsafeCoerce the result will be whatever the representation of "abcd" in memory is when interpreted as an integer.
How are functions represented in memory?
In Haskell, all complex objects including functions are internally represented as a pointer. This is a number in binary that "points" to a specific location in memory. This is because we want to pass these values by reference, since copying the whole thing is expensive, and since Haskell disallows mutation we can with no problem.
However simple objects like ints are passed by value since they are so small that copying them is about as expensive as copying a pointer would be. So they are not represented as pointers but rather just whatever structure they are.
So if we use unsafeCoerce from a complex object, say a function, to a simple object, say an Int, what happens is that the pointer to the function gets converted to the simple object. And the value of that simple object is dependent only on where the complex object is located not anything about what it is.
Address Space Layout Randomization
Many software vulnerabilities rely in part on being able to find particular functions in computer memory to access them. For these techniques you create some malicious code somewhere in memory (this can be done a few ways) and then by hijacking the stack pointer convince a program to run your code. In order to combat these exploits many systems implement something called Address Space Layout Randomization or ASLR. With ASLR key components are placed randomly so that their locations cannot be predicted. This means even if you do get control of the stack pointer it is hard to find where your malicious code is placed. ALSR is not the only technique used against these attacks but it is one we care about.
For Linux systems you can check of ASLR is on using
cat /proc/sys/kernel/randomize_va_space
Or since this is code-golf:
sysctl -anr "e_v"
There are three levels of security here 0 for off, and 1 and 2 for varying levels of on. My computer has this set to 2 (and your computer probably does too).
You can also set this. However do not do this unless you know what you are doing. Please do not mess with your kernel (unless you know what you are doing). For this reason I'm not going to include the command to do this, but you can look it up online or figure it out from the commands I already gave.
What this means for us is that the locations for objects allocated by Haskell at runtime is random or at least non-deterministic. This means that when we take a complex object like a function and convert it to a simple object like an Int the value of that object is random too.
The program
So that's what our program does. We coerce a function, (+) because it is short. We wrap this in a list and print it using putStr. Since putStr expects a string the compiler infers that the output of unsafeCoerce(+) must be a Char, which is a simple type.
So we end up printing a random one character string.
A more normal solution, 44 bytes
import System.Random
main=randomIO>>=putChar
For completion sake this is the "normal" Haskell approach. It is slightly shorter but far more boring.
CJam, 2 bytes
- You can rely on the program being run at a different (unknown) time each execution.
Yeah, that one. et is a single built-in that returns the array [YYYY M D h m s ms W Z], printed as YYYYMDhmsmsWZ.
Trigger, 14 bytes
ABAAA AAB B
A NOT the value of the A trigger, making it one
B NOT B
AAA Print "A"
AAB Go to the nearest B in the program. If it is the same distance, it picks it randomly. This can go to the NOT B command or go to the next B command, running the print A or ending the program, respectively.
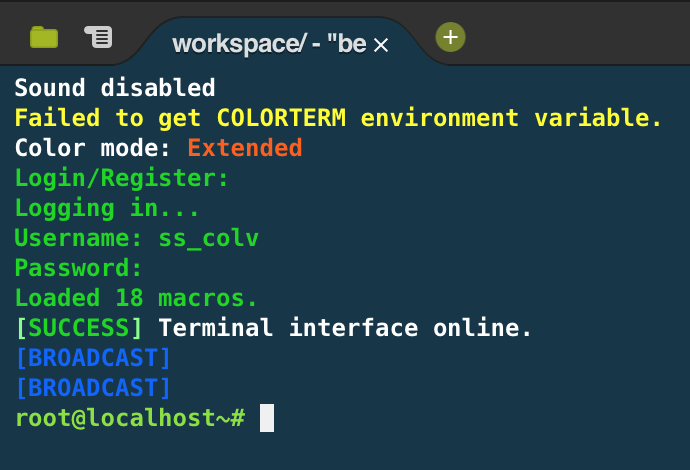
Intercept 1.1, 37 bytes
Prints newlines to the terminal. You'll probably have to leave this one overnight, as there is a delay of 5-15 minutes (it's random!) between each newline. Note that while you can determine what is being printed, you can't determine how often it's being printed.
Input is marked with a >>. The command prompt is the empty >>.
Assuming a system with only TZ_INFECT installed...
>> malware bm bitminer
creating bm (bitminer)
... wait a minute ...
finished creating bm (bitminer)
>> software install 1
Success
bm installed
...wait...
(newlines)
>>
Note that I'm using a custom client that prefixes [BROADCAST] to all broadcast events.
How???
TZ_INFECT is Intercept's malware generator. We can generate a bitminer by running malware <name> bitminer. This will create a new piece of software with the given name of type bitminer
We then install the bitminer: software install <index>, where index is the 0-based index of the software as given by software list. This is why I made sure the only piece of software on the system was the malware generator. This places our new bitminer at index 1.
There is a bug in the implementation of bitminer that results in an empty broadcast event to be sent to the client whenever bits are generated. Since bits are generated at random intervals, the broadcasts are sent at random intervals. Voilia, non-deterministic output!
Note: the newlines are harder to detect using the official game client, but you can see them by running a command and watching the newlines slowly push the resulting output off the screen.
Screenshots coming in a few hours while I wait for the output.
After 20 minutes (the [BROADCAST] is a newline):
Gol><>, 3 bytes
x1h
The 'x' is a randomizer for the direction of the pointer, the 1 pushes a 1, and the h outputs and halts.
Rust, 28 bytes
fn main(){print!("{:p}",&1)}
Takes a reference to a temporary 1 and prints the address.
Rust, 17 bytes
fn main(){0-1u8;}
Try it online! (requires the -A const_err compiler flag)
This is a bit sketchier, and I'm not sure whether it counts. The non-deterministic output is to STDERR, and the non-determinism arises only based on the value of an environment variable.
This program attempts to compute 0 - 1, where both integers have type u8 (the default is i32, which won't cause an overflow because it's signed). By default, Rust compiles the file in debug mode, in which arithmetic overflow causes a panic instead of wrapping. When a program panics, it will print a stack trace if the environment variable RUST_BACKTRACE is set to 1, hence the non-determinism.
Lost, 7 bytes
@%"
///
Since Lost starts the pointer in a random place facing a random direction, it's refreshing not making the output deterministic for once. I think this is the optimal solution since you need the @ and % in order to end the program, the " to push stuff to the stack at random, and the /// to avoid infinite loops.
Wumpus, 4 bytes
UFO@
Outputs a uniformly random choice of 2, 5 or 8.
Explanation
Apart from a regular stack, Wumpus also has 20 registers which are arranged around the faces of an icosahedron. You can imagine the icosahedron as a d20 resting on a table: the face touching the table is the "active" face (i.e. the register that can currently be interacted with). Also, every face has an index from 1 to 20. Initially, the active face is 1 and the three adjacent faces are 2, 5 and 8 (see the README in the Wumpus repo for the full net).
U Randomly tip the icosahedron onto one of the three adjacent faces, i.e.
change the active faces to either 2, 5 or 8.
F Push the index of the currently active face.
O Output as a decimal integer.
@ Terminate the program.
Alternatively:
DFO@
This one completely randomises the orientation of the icosahedron, so it prints a random number from 1 to 20, inclusive.
Kotlin script (.kts), 12 bytes
print(Any())
Any is a compile-time time wrapper for Object, default toString() of any object is class name@hashcode. Probably the shortest solution that runs on the JVM.
If .kts is cheating:
18 bytes: fun a()="${Any()}" (forgot functions are a valid answer)
38 bytes: fun main(a:Array<String>)=print(Any())
Chip, 2 + 3 = 5 bytes
+3 bytes for -w
g?
Gives infinite-length output. Each byte of output is independent, and is either NUL \x00 or '@' \x40.
There are eight equivalent Chip programs that are like this, from a? (which prints \x00 or \x01) to h? (which prints \x00 or \x80). g? is just the most visible option.
For each of these programs, the letter a through h defines the index of a bit of the output, and ? produces a random value to set it to. The two elements may be provided in any order; they must only touch each other on a 2D plane.
Try it online! The TIO includes the -cN flag. This flag is not necessary, but cuts off the program after N bytes. Try without the cutoff if you wish, but TIO's limit is at 128KiB.
Retina, 3 bytes
?&`
Yay, Retina can finally compete in challenges that require randomness! \o/
Explanation
?& is a compound stage which executes its child stage with a 50% probability. That child stage is itself a Count stage, which counts the number of empty matches in the empty input (1). So if the child stage is run, the result is 1, if it isn't, then the empty input remains unchanged and we get an empty string.
A fun alternative for the same byte count would be:
?+`
This one uses a random loop (which uses a coin toss before each iteration to decide whether to continue). This one has a 50% chance of printing an empty string, 25% of printing 1 (one iteration) and a 25% chance of printing 2 (two or more iterations).
INTERCAL, 0 2 bytes (0+2 for command flag)
Try it online! (I don't know if the TiO compiler reproduces this functionality correctly)
This is not a valid INTERCAL program, so attempting to run it gives Error 778 - UNEXPLAINED COMPILER BUG. However, when INTERCAL is run without the -b command flag, there is a small chance that it doesn't run and throws Error 774 - RANDOM COMPILER BUG. So if errors count as output for this challenge, then INTERCAL might actually be good for something!
INTERCAL, 17 bytes
DO %9 READ OUT #5
This is a more standard approach. It has 9% chance of printing V before terminating (with an error, but it gives the output, so who cares?)
Chip-8, 4 bytes
0xCFFF 'RND vF,FF
0xFF18 'LD ST,vF
This plays a sound for between 0 and 4.25 seconds. The seed always starts at 0, but it updates during the display interrupt which has a tiny chance of happening before the randomizer call, I hope.
BrainFlump, 5 bytes
:+:;.
Outputs either a NUL or SOH character
Explanation
BrainFlump is the latest iteration of BrainFl* languages having different memory models (BrainFlak is a stack, BrainFlueue is a queue, etc)
In BrainFlump, memory consists of a Cell and a Dump.
The Cell is a single numerical value, and the Dump is an unordered collection of numerical values.
When the program starts, the Dump is empty, and the Cell is 0.
: Push the Cell's value to the Dump
+ Increment the Cell
: Push the Cell's value to the Dump
; Pop a value from the Dump (randomly) to the Cell
. Print the Cell's value as an ASCII character
The Cell's value will either be 0 or 1, and as it's printed as an
ASCII character, this results in NUL or SOH
Java 7, 33 30 27 bytes
int a(){return hashCode();}
Because Java.
Add++, 6 bytes
The most random I could get for 6 bytes
+9 Set the accumulator to 9
R Set the accumulator to a random integer between 0 and 9
O Output the result
I could change R to R-9 to double the randomness for 2 extra bytes.
Baby Language, 0 bytes
I didn't submit this originally because I thought it postdated the question. I was wrong; the language did have an interpreter created in time. It's also probably the least cheaty 0-byte solution I've seen (given that a 0-byte program is specified to do exactly what the program asks, and not for the purpose of cheating on golfing challenges).
Baby Language is specified to ignore the program it's given and do something at random. (The interpreter linked on the Esolang page generates a random legal BF program and runs it.) That seems like a perfect fit for this challenge.
C (gcc), 18 bytes
f(){printf("%d");}
This one may be difficult to test since TIO will give you a cache hit. Just add some whitespace and try it again.
C, 19
f(a,b){putchar(b);}
In C the second declared variable in a function's arguments is random based on memory. Assuming the arguments were not actually declared, i.e. you just called f();.
So this function can be simply called with no input-arguments. That is, just: f(); and the output will be a random character.
Try it online! (Note: output might be an unprintable character, run the program a few times to see variation, you should get more printable characters than non-printable characters)
C, 22 bytes
f(){putchar(time(0));}
Alice, 4 bytes
2Uo@
Prints a single byte, either 0x00 or 0x01, with 50% probability each.
2 Push 2.
U Get a random integer in [0,1].
o Output that integer as a byte.
@ Terminate the program.
tcl, 3
Must be run on an interactive shell
pwd
Gets the current working directory.
Or alternatively
pid
Gets the current process identifier
Demo: Go to https://www.tutorialspoint.com/execute_tcl_online.php and in the green area, type
tclsh
Then type
pwd
and
pid
Commodore 64 Basic, 4 bytes
1S|0
PETSCII substitution: | = SHIFT+Y
The zero page of a Commodore 64 is an area of 256 bytes of memory that can be accessed faster than the rest of RAM. Consequently, programs (such as the BASIC interpreter) use it for frequently-accessed data, and the CPU itself stores some of its internal state here. The contents are subject to change without notice.
The BASIC program above, ungolfed, is 1 SYS 0, ie. transfer execution to memory location 0. This starts executing the zero page as code. Normally, when the BASIC interpreter starts running a program, the first 16 bytes are
2F 37 00 AA B1 91 B3 22
22 00 00 4C 00 00 00 00
so SYS 0 would execute the following
00: ROL-AND $37,A - Undocumented opcode: rotate the value at memory location 0x37 left, and store the result in the accumulator
02: BRK - Call the interrupt vector
The overall result is to output the BASIC READY. prompt and return control to the user. However, memory location 0x00 is the CPU's I/O direction register, and memory location 0x01 is CPU's I/O address register. If you've done something that changes these before running the program, the results can be unpredictable, ranging from outputting garbage to locking up the computer (the 0x22 usually contained in memory location 0x07, if executed as an instruction, is an undocumented HALT opcode).
Alternatively, a more reliably unpredictable program is the four-byte
1?TI
Prints the elapsed time, in jiffies (1/60 of a second), since system power-on.
C#, 72 bytes
It's alot longer than the other C# answer but hey, different approach and fully functioning console application. Why not?
Golfed
using System;class P{static void Main(){Console.Write(Guid.NewGuid());}}
Ungolfed
using System;
class P
{
static void Main()
{
Console.Write(Guid.NewGuid()); //Create a new random GUID and print it
}
}
SmileBASIC, 6 bytes
?TIME$
Prints the current time.
TI-Basic, 2 bytes
Very similar to this answer. The getTime token is two bytes and is located at EF 0A.
getTime
PowerShell, 4 2 bytes
(crossed out 4 still looks like 4)
ps
This is the alias for Get-Process which will output the current process listing as a table, including handles, private memory, CPU time, etc.
Execute it via something like the following:
C:\Tools\Scripts\golfing>powershell.exe "ps"
ForceLang, 11 bytes
random.rand
A function that, when called with no arguments, produces a random rational of the form n/2^80, where n is an integer on [0,2^80-1].
(If you give it a positive integer argument m [which must be strictly less than 65536, not that you'll ever reasonably need to go nearly that high] it will produce a random rational of the form n/2^m, where n is an integer on[0,2^m-1])
Ruby, 14 bytes
p ?..object_id
Returns object id of the string '.'
Shell, 2 bytes
ps
Explain: the PIDs returned are not going to be the same each time.
MATLAB, 3 bytes
why
why provides answers to almost any question. A few examples:
why
The programmer suggested it.
why
To fool the tall good and smart system manager.
why
You insisted on it.
why
How should I know?
This is shorter than any rand function I can think of.
JavaScript, 4 bytes
Date
A function which returns the current date/time. I think this is the shortest it will get...
Explanation
Since this seems to be causing a lot of confusion as to why it's valid, I'll try to explain.
In JavaScript, a function entry is valid if it can be assigned to a variable and called like a function. For example, this function is a valid entry:
function(){return Date()}
Because it is a function that can be assigned to a variable like so:
f=function(){return Date()}
And then run with f() as many times as necessary. Each time, it returns the current date/time string, which has been ruled non-deterministic by the OP.
This ES6 arrow function is also valid:
_=>Date()
It can be assigned with f=_=>Date(), then run with f() like the other one.
Now, here's another valid entry:
Date
Why? Because just like the other two entries, it can be assigned with f=Date and then called with f(), returning exactly the same thing as the other two. Try it:
var f = Date<button onclick="console.log(f())">Run</button>Lua, 9 bytes
print({})
Outputs the internal address of the Lua table object:
table: 0x2370ab0
If you're running from the interactive interpreter, you can use just 3 bytes:
> ={}
table: 0x23719c0
Pyth, 2 bytes
O0
Explanation:
0 0
O Random float in [0, 1)
It's that, when O has 0 as its argument, it simply returns a random float between 0 and 1, exclusive.
Let's do it just for the heck of it!
Also, it seems that this can be sorta retro (thanks to 34718/mbomb007):
Pyth, 2 bytes
OT
Explanation:
T 10
O Random integer in [0, 10]
Groovy, 9 bytes
{print{}}
Outputs:
Script1$_run_closure1@2c8ec01c
Because it outputs the memory address of the closure it is non-deterministic.
Minecraft, 2 bytes
/r
Must be written into chat when playing on multiplayer servers. Will throw an error if you hadn't messaged (/tell) anybody recently. Otherwise, shows both players a random message.
Note: I'm not really sure if this is a legit solution :)
Minecraft, 4 bytes (+2 blocks)
help
Ties with another Minecraft answer from @Pavel
This is based on Minecraft's Easter egg:
When you type
helpor/helpin a Command block, a random message starting with "Searge says:" is displayed, for example "Searge says: Ask for help on twitter". Here is a full list of messages.
C++, 26 19 Bytes
std::cout<<new int;
Returns a different memory address each time it's run
Minecraft, 5 4 bytes
op 8
Used by typing into a server's console or a command block and giving it power. Can be run from the chat interface by prepending a /.
Usually this does nothing, but if there's a player with the username "8" on the server, they will be given operator permissions. Note that while Minecraft normally requires usernames to be 3 characters long, some accounts with shorter name lengths were created before this restriction.
The version that can be demonstrated to be non-deterministic without one of these usernames or risk of giving a user operator permissions is here:
me @r
Displays a message to everyone, the message being the username of a random player. The op command only takes a string literal, not any script that returns a string.
The me command wouldn't really work for the first example, it would display "<your-username> 8". When run from a command block, it wouldn't be deterministic since all command blocks have the same "username" but running it from the chat interface would require the / for one extra byte.
Inform 7, 6 bytes
x is y
This isn't a valid Inform 7 program, since neither "x" nor "y" has been defined. So this throws an error.
However, some of Inform 7's error messages—including this one—are randomized. So the text it prints is technically non-deterministic.
A few possible outputs include:
Problem. The sentence 'x is y' appears to say two things are the same - I am reading 'x' and 'y' as two different things, and therefore it makes no sense to say that one is the other: it would be like saying that 'Adams is Jefferson'. It would be all right if the second thing were the name of a kind, perhaps with properties: for instance 'Virginia is a lighted room' says that something called Virginia exists and that it is a 'room', which is a kind I know about, combined with a property called 'lighted' which I also know about.
Problem. The sentence 'x is y' appears to say two things are the same - I am reading 'x' and 'y' as two different things, and therefore it makes no sense to say that one is the other: it would be like saying that 'Adam is Eve'. It would be all right if the second thing were the name of a kind, perhaps with properties: for instance 'Land of Nod is a lighted room' says that something called Land of Nod exists and that it is a 'room', which is a kind I know about, combined with a property called 'lighted' which I also know about.
Problem. The sentence 'x is y' appears to say two things are the same - I am reading 'x' and 'y' as two different things, and therefore it makes no sense to say that one is the other: it would be like saying that 'Clark Kent is Lex Luthor'. It would be all right if the second thing were the name of a kind, perhaps with properties: for instance 'Metropolis is a lighted room' says that something called Metropolis exists and that it is a 'room', which is a kind I know about, combined with a property called 'lighted' which I also know about.
Problem. The sentence 'x is y' appears to say two things are the same - I am reading 'x' and 'y' as two different things, and therefore it makes no sense to say that one is the other: it would be like saying that 'Aeschylus is Euripides'. It would be all right if the second thing were the name of a kind, perhaps with properties: for instance 'Underworld is a lighted room' says that something called Underworld exists and that it is a 'room', which is a kind I know about, combined with a property called 'lighted' which I also know about.
Ceylon (on JVM), 22 bytes
()=>system.nanoseconds
This turned out surprisingly difficult.
At first I thought I cold use the .hash attribute of all objects (corresponds to Java's .hashCode() when running in the JVM), but it turns out that most objects I can write in a literal way have their .hash attribute overridden, returning a deterministic value.
For example, [] (the empty tuple) or {} (the empty iterable) are both the same object, and which inherits List.hash, which returns 1 in this case. For strings (like ""), characters (c) or numbers (like 3 or 2.5) of course the hash needs to be deterministic, same for true and false (0, 99, 3, 1074003968, 1231, 1237, respectively).
The base class Basic, which has the Java-like hash code implementation (assumedly based on the memory address?) is abstract, so I can't use Basic().hash (nor Object().hash – also abstract, and here even the method is not implemented). So let's create a new class, create an instance and take its hash code?
class E() {}
function f() => E().hash;
shared void run() {
print(f());
}
This always outputs 1116094714 whenever I execute this program. (Adding other statements which allocate memory before the print line changes the result – still deterministically, though.)
Ceylon also supports anonymous classes as object expressions. Those can extend classes or implement interfaces and have own code, but the most minimal variant is just object{}:
shared void run() {
function f() => object{}.hash;
print(f());
}
Still the same result 1116094714, though.
Another idea was to use the hash code of a class or function reference. (Those are normal objects, I thought.) But trying to use run.hash (or f.hash) gives a compiler error:
error: direct function references do not have members
We can work around this by assigning this function reference first to a value, which will create an object of a (hidden) anonymous class:
shared void run() {
value x = run;
value y = run;
print([x.hash, y.hash]);
}
This prints two different values, but the same ones ([762384154, 690052870]) each time I run the program. Still deterministic.
So, using any hash code will not bring us forward (and I suppose that the other JVM answers here with .hashCode() would have the same problem on my JVM implementation). Same with printing an object with the default .string implementation based on .hash.
There is no random number facility in ceylon.language, so using either ceylon.random or Java's java.util.Random (or java.lang.Math.random()) needs an import, which increases the size more than I want to tolerate for a codegolf answer. Here is an example:
import ceylon.random { ... }
shared void run() {
print(randomize{1,2});
}
So let's look at what we have in ceylon.language. There are four top-level objects which allow access to the environment:
operatingSystem– name, version, path/file separator, newline.process– command line arguments, system properties, environment variables, input/output.runtime– whether we are on JVM/JS/Dart, version info, and stuff like bit sizes. Nothing which will change between runs of the same program in the same VM.system– ah, here we go. Beside locale, character encoding and time zone offset we also have:millisecondsnanoseconds
Both will change with each call of a program, and the latter one is shorter.
So here we have an anonymous function returning different values:
() => system.nanoseconds
If we want a named function, its definition can look like this:
Object n()=>system.nanoseconds;
(It actually returns Integer, but that is one character longer than Object.)
ASP VBScript, 43 bytes
<%=createobject("scriptlet.typelib").guid%>
Outputs a unique ID like {52076580-3151-4EE7-AAFD-D975CD141EE4} based on current date/time. ↑
TI-83 Hex Assembly, 4 bytes
PROGRAM:ND
:AsmPrgm
:EF0A45
:C9
Run it with Asm(PrgmND). Calls the _PutS system library call (0x450a), but because it doesn't set HL it will print whatever HL pointed to last, usually a lot of garbage text.
I count this as 4 bytes, because each pair of hex digits is one byte.
Java2K, 9 bytes
I don't recommend trying to write an approximation of a deterministic program in this language.
11 6/*/_\
This function has a 90% chance to return 1, otherwise it will return a random number. 11 6 is the name of the division function. A function is called like <name>/<arg0>/<arg1>\. Basicaly every function returns the "correct" result 90% of the time, or else a random number.
The token * is replaced by a random number, say 203. The _ token is replaced by the previous argument, i.e. 203. So, this function will divide 203 by 203 which has (see below) a 90% chance of returning 1.
huh?, 0 bytes
An empty program still produces output. The last lines of the Python interpreter that are executed:
print "..."
f = open('Notes.txt', 'w')
f.write(time.strftime("%c") + " - The user tried to give me commands again. I still have no idea what they are talking about...\n")
At the end of a program, the Python interpreter will print ..., then it will create/open a text file called Notes.txt and write a string which contains the current time in front.
Minkolang v1.5, 4 bytes
lhN.
l pushes 10. h pushes a random integer from 0 to 10, N outputs it and . ends program. Simple, eh?
PHP 10 bytes
<?=rand();
Prints a random number between 0 and getrandmax(). Which may vary based on what computer it's run on.
PHP, 12 bytes
<?=uniqid();
Outputs a unique ID 583f4da627ee3 based on the current time in microseconds. ↑
Microscript II, 1 byte
R
Produces a random 64-bit float on [0,1).
Another one-byte solution would be C, which produces a new continuation object, whose timestamp (which the reference implementation includes in its string representation) will be nondeterministic.
T-SQL 15 bytes
print getdate()
Thue, 17 bytes
a::=
a::=~1
::=
a
Randomly prints either nothing, or the digit 1.
C#, 36 22 bytes
a=()=>a.GetHashCode();
Yay.
Mouse2002, 7 bytes
&RAND !
C89 with GCC/Clang, 20 bytes
The other C solution just segfaults every time when built with GCC or Clang. This, though.
main(n){puts(&n+1);}
Which looks like:
$ for _ in `seq 1 50`; do ./test_89; done
���z�U
�VW��U
�F��U
�v�f2V
��FV
���*=V
�6���U
�20wU
��
�+V
�6
�U
��V�uU
�v��V
���K�U
��7�qU
�6S�jU
�&�WU
��wV
��6l�U
���U
�F�ߨU
�f���U
���s7V
�f��?V
��;B�U
�;��U
��GV
�� ��U
�vKV
�V?]wU
�����U
��.�U
�v"�XU
��uhpU
��LD�U
�����U
�6X�U
��M�.V
�69��U
��ԤV
���U
����U
�vx4.V
�֝+xU
�F��U
�֤BQV
��#�U
���1^U
����sU
��4�U
��AݗU
Quite a lot of unprintable junk but it's nondeterministic!
Microscript, 2 bytes
r9
Produces a random integer on [0,8]
Randwork, 11 bytes
Uses the Randwork+ instruction set, because that's the only specification with an existing interpreter.
Do anything
This statement executes a random instruction from the instruction set. There is a 7/28 (25%) chance of non-empty output. I calculated the probability by viewing the source code of the interpreter. The instructions that can produce output are:
Write the ASCII equivalence of a random byte
Beep
Write the ASCII equivalence of byte 1
Write the ASCII equivalence of byte 2
Write the ASCII equivalence of byte 3
Write the ASCII equivalence of byte 4
Display the Hello World message
Bytes 1-4 have not been set, so output of any of them will be a NUL byte. The 7 possibilities of non-empty output are (in corresponding order):
\x?? - a random byte
\x07 - the bell character (beep)
\x00 - NUL
\x00
\x00
\x00
Hello world
Bash (procps-ng), 2 bytes
ps
$$ is also a solution.
R, 7 bytes
The Student t Distribution
rt(1,1)
The Exponential Distribution
rexp(1)
Two options how to generate a random number with the shortest code.
Actually, 1 byte
G
Good old rand(). In Python 3, 2500 random bits from the system's cryptographically-secure randomness source (getrandom() for Linux, /dev/urandom for *NIX, or CryptGenRandom for Windows) are used for the seed, falling back on the current UNIX time (as precisely as possible for the given platform - at minimum, 1-second precision) if such a source of randomness is not available.
QBIC, 4 bytes
?_r|
This generates and prints a random number between 0 and 10. QBIC uses the classical RANDOMIZE TIMER at the start of execution to set the RNG.
MATL, 1 byte
r
Uniform random number generator between 0 and 1. The seed is randomly set for each execution of the program. Try it online!
Marbelous, 5 bytes
FF
??
Prints a single random byte. FF creates a marble with value 255. That marble falls through the random number generator ?? which replaces the marble's value with a random value between 0 and 255 inclusive. When the marble falls off the bottom of the board, it gets printed to STDOUT as a byte.
Brachylog, 3 bytes
9$?
Explanation
$? is the random number predicate. When given an integer as input (here, 9), its output will be unified with an integer between 0 and 9 uniformely at random.
Befunge (-93 and -98), 3 bytes
?.@
The ? sends execution in a random direction. If it goes up or down, it loops back to the ? and rerolls. If it goes left, the program wraps round to the @ and thus exits without printing anything. If it goes right, it prints 0 (the output produced by . when the stack is empty) and then exits on the @.
Swift 3, 13 bytes
print(Date())
APL, 2 bytes
?9
This uses APL's roll (?) operator. The program prints a pseudo-random number between 1 and 9.
Perl 6, 13 bytes
put Bool.pick
Clojure, 4 bytes
rand
The obvious answer. rand is a core function that returns a floating-point number between 0 and 1 (exclusive) when called without any arguments.
I don't think it gets any shorter than this in Clojure.
PHP, 10 Byte
<?=time();
This prints the current Unix time which – of course – isn't random but changes when you call the program several times. The output I just got is 1480548602.
C, 25 21 bytes
Thanks to pseudonym117 for saving 4 bytes.
main(i){putchar(&i);}
Compiled with gcc -o test lol.c (yeah I'm quite original with my file's name...), and ran with ./test.
It does what it says: prints the character corresponding to the memory address of i, which is defined at runtime, so it should be non-deterministic.
R, 1 byte
t
Outputs the function's source code and a memory pointer address which changes with every (re-)start of R.
Cubix, 3 bytes (non-competing)
@OD
Outputs a random positive number of zeroes. Non-competing because I added D just a few minutes ago. Before it was added, there was absolutely no way to randomize anything in Cubix.
How it works
Before the code is run, it's padded with no-ops . and formed into a cube net. Here's what the net for this particular program looks like:
@
O D . .
.
Now the code is run, starting on the left-most face and heading to the right.
First, O outputs the top item on the stack as a number. At the beginning of the program, the stack is an infinite fount of zeroes, so this prints 0.
Next, D sends the IP (instruction pointer) in a random direction: possibly up to the @ which ends the program, and possibly back to the O which prints another 0. This continues until whenever the IP hits the @.
@DO and OD@ also work, each printing zero or more zeroes.
x86/amd64 machine language (Pentium or higher), 3 bytes
0: 0f 31 rdtsc
2: c3 retq
This uses the RDTSC instruction that may not be available on older processors. To test, try the following C program on Linux x86/amd64
#include <stdio.h>
int main(){
for( int i = 0; i < 10; i++ ) {
printf( "%d\n", ((int(*)())"\x0f\x31\xc3")() );
}
}
Or try it on Ideone.
Jelly, 2 bytes
9X
Idk if this works. I've never done anything in jelly before, and I'm on my phone right now.
Int from 0 to 9.
Batch, 6 4 bytes
time
Needs to be run with <nul which is apparently permissible.
Mathematica, 6 bytes
Date[]
Pretty self-explanatory. (This function was superseded by DateList[] in later versions, but Date[] still runs.)
For 8 bytes one can also use Random[] (itself a legacy function).
><>, 4 3 bytes
(crossed out 4 still looks like 4)
0nx
Outputs some amount of 0's.
On an empty stack n throws an error and terminates the program. x chooses a random direction for the stack pointer. This means that for each 0 printed, there is a 50% chance for the program to exit.
sh + procps, 1 byte
w
This is the shortest solution I'm aware of that works via calling into external executables. procps is the responsible package for reporting information about the current system state (ps and friends), and is installed on most Linux distributions by default; w is the shortest-named command in it, and returns information about the logged-in users, but also some nondeterministic information like uptime.
Japt, 1 byte
Ð
How it works
When Japt is compiled to JavaScript, it replaces Ð with new Date(. The close-paren is automatically added by the interpreter, and the result of the last expression is automatically printed, so this prints the current date/time.
An alternate solution would be Mr, which uses Math.random. Japt also has the variable K set to Date (no clue why I did that, it's almost entirely useless), which I guess makes K a valid function entry.
Python 2, 29 bytes
import os
print os.urandom(9)
Sadly not the first time writing code on a smartphone.
JavaScript, 8 bytes
Date.now
This evaluates to a function whose return value is nondeterministic, and conveniently doesn't actually need to be bound to anything specific to work.
WinDbg, 1 byte
#
Wow! Never expected a 1 byte solution from WinDbg!
# searches for a disassembly pattern, but since there's no parameters, it looks to just return the next assembly instruction in whatever dump/process you're attached to. Not sure the logic for setting the initial address, but it does.
Sample output:
0:000> #
Search address set to 75959556
user32!NtUserGetMessage+0xc
75959556 c21000 ret 10h
0:000> #
user32!NtUserGetMessage+0xf
75959559 90 nop
0:000> #
user32!NtUserMessageCall
7595955a 90 nop
0:000> #
user32!NtUserMessageCall+0x1
7595955b 90 nop
0:000> #
user32!NtUserMessageCall+0x2
7595955c 90 nop
0:000> #
user32!NtUserMessageCall+0x3
7595955d 90 nop
0:000> #
user32!GetMessageW
7595955e 8bff mov edi,edi
0:000> #
user32!GetMessageW+0x2
75959560 55 push ebp
0:000> #
user32!GetMessageW+0x3
75959561 8bec mov ebp,esp
0:000> #
user32!GetMessageW+0x5
75959563 8b5510 mov edx,dword ptr [ebp+10h]
Shellscript (as implemented by ttyrec), 0 bytes
OK, here's a version of this idea that uses an interpreter that can actually be programmed with.
The ttyrec command by default just passes everything it sees on standard input to a shell, and thus obeys our definition of a programming language (it's Turing-complete, because bash is; it's basically just an alternate front-end to bash, and so is basically a shellscript interpreter that can be used to program with). However, it also creates a file ttyrecord containing a recording of the shell's output, and that file starts with the current time, in binary (and is also affected in some ways by the system's CPU and swapping load, as it tries to separate the output into frames). Thus, it produces a file with nondeterministic content as output.
Labyrinth, 5 bytes
v
!
@
Either prints 0 or nothing (50% chance each).
There is a very specific case in which Labyrinth exhibits random behaviour:
- There must be a wall in front of the instruction pointer and behind it.
- There must be a non-wall left and right of the instruction pointer.
- The current top of the stack must be zero.
If all of those conditions are met, the direction the IP moves in is chosen (uniformly) randomly. The cherry on top is that those three conditions are impossible to meet in regular control flow, which means unless you modify the source code at runtime.
(This may seem a bit arbitrary, but it's actually the most consistent behaviour I could find for these conditions, since normally the direction of the IP always depends on the previous direction, its neighbours, and the sign of the top of the stack, and this seemed like an elegant way to include a source of randomness in the language.)
With the help of the source code rotation instructions (<^>v) it's possible to bring the IP into this situation. One such example is seen at the top. The IP initially points east and starts at the top. The v rotates the current column so that we get:
@
v
!
The IP moves along with this rotation so that it's still on the v, pointing east. All the conditions are fulfilled now, so the IP will either go up or down randomly. If it goes up, the program terminates immediately. If it goes down, it prints a zero, rotates the column again, and then terminates.
There are three other programs making use of this (one which also prints 0, one which prints 00 and one which prints 000):
v
@
!
"
>@!
"
>!@
(Actually there are a lot more than three other programs, because you could also use . instead of ! to print null bytes, or replace that " with a large variety of commands, but I believe they all work essentially the same.)
Zsh, 5 bytes
<<<$$
Prints PID.
05AB1E, 2 bytes
žd
Outputs current microseconds from the executing machine's internal clock.
Or you could do something like this...
05AB1E, 3 bytes
A.r
Outputs a randomly shuffled lower-case alphabet.
Or this also works:
A.R
Outputs a random letter from the alphabet.
Or this also works, and is cooler:
05AB1E, 9 bytes
"ž"A.RJ.V
Outputs randomly one of these:
ž 23 > ža push current hours
žb push current minutes
žc push current seconds
žd push current microseconds
že push current day
žf push current month
žg push current year
žh push [0-9]
ži push [a-zA-Z]
žj push [a-zA-Z0-9_]
žk push [z-aZ-A]
žl push [z-aZ-A9-0_]
žm push [9-0]
žn push [A-Za-z]
žo push [Z-Az-a]
žp push [Z-A]
žq push pi
žr push e
žs pop a, push pi to a digits (max. 100000)
žt pop a, push e to a digits (max. 10000)
žu push ()<>[]{}
žv push 16
žw push 32
žx push 64
žy push 128
žz push 256
Python 2, 11 bytes
print id(1)
Perl, 5 bytes
say$$
Outputs the process ID and a newline.